What is a Trusted Platform Module (TPM)?
A Trusted Platform Module (TPM) is a dedicated microcontroller designed to secure hardware by integrating cryptographic keys into devices. It provides a hardware-based root of trust for security-critical functions like disk encryption, password protection, and secure boot. For industrial and commercial computing, a TPM is essential for ensuring system integrity, protecting sensitive data, and meeting compliance standards for cybersecurity.
Key Specifications and Technical Details
A TPM is a separate chip or firmware-based security solution that works alongside the main processor. Key technical features include:
-
Cryptographic Processor: Generates, stores, and limits the use of cryptographic keys.
-
Hardware-based Security: Isolates security functions from the main operating system, making it resistant to software-based attacks.
-
Platform Integrity Measurement: Verifies the boot process to ensure no unauthorized changes have been made to the system firmware or OS.
-
Secure Storage: Provides a protected area for storing passwords, certificates, and encryption keys.
-
Remote Attestation: Allows a system to prove its health and configuration to a network service securely.
Use Cases and Applications
TPM technology is critical in environments where data security and system integrity are non-negotiable.
-
Industrial Automation: Securing control systems and operational technology (OT) networks from unauthorized access.
-
Digital Signage & Kiosks: Protecting content and preventing tampering in public-facing devices.
-
Healthcare: Safeguarding patient data and ensuring compliance with regulations like HIPAA.
-
Financial Services & Retail: Securing point-of-sale (POS) systems and ATMs against skimming and data theft.
-
Government & Defense: Meeting stringent security requirements for sensitive communications and data handling.
Comparison: TPM 1.2 vs. TPM 2.0
| Feature | TPM 1.2 | TPM 2.0 |
|---|---|---|
| Cryptographic Algorithms | Primarily RSA & SHA-1 | Supports modern algorithms (RSA, ECC, SHA-256) |
| Flexibility | Fixed specification | More flexible, vendor-customizable commands |
| Key Storage | Limited hierarchy | Enhanced hierarchical structure |
| Mandatory for Windows 11 | No | Yes (for most devices) |
| Modern Security Standards | Outdated | Designed for current and future threats |
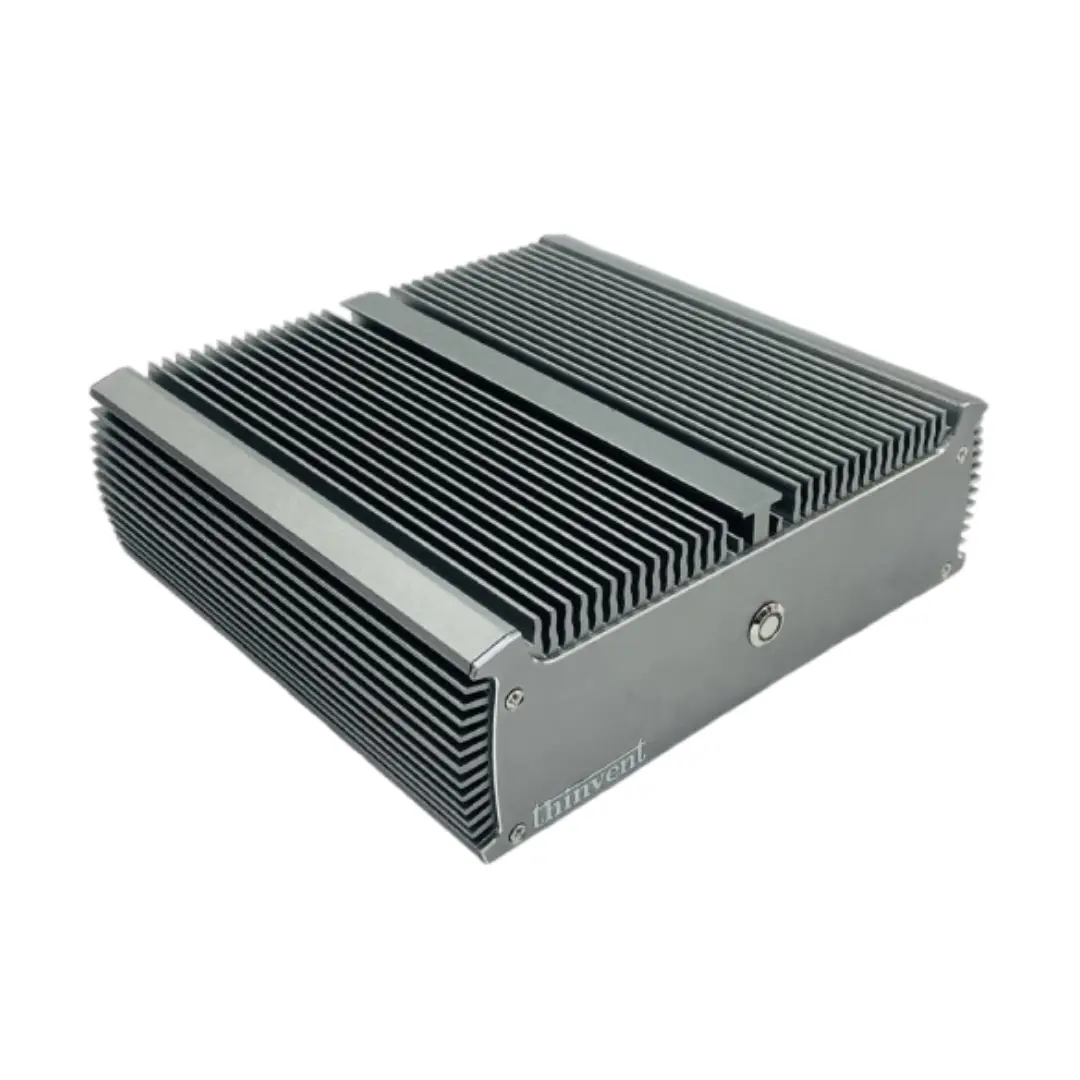
Thinvent Products Featuring TPM Technology
Thinvent integrates TPM security across its range of industrial computing solutions to deliver trusted platforms for demanding environments. Our fanless Mini PCs, Thin Clients, and All-in-One systems are available with TPM 2.0 modules, providing a hardware root of trust for secure boot, device identity, and data encryption. Whether for edge computing in manufacturing, secure digital signage, or reliable kiosk applications, Thinvent's TPM-enabled devices ensure your operations are protected against unauthorized access and cyber threats. Explore our catalog to find the secure, reliable computing platform tailored to your specific industrial needs.